Spotify is currently the number one music service on all platforms, and these include not only iPhone and Android, but also CarPlay and Android Auto.
According to information shared by the company itself in late October, Spotify now has 320 million monthly active users and no less than 144 million subscribers paying for premium access to its content.
But this doesn’t necessarily mean Spotify is also the most secure service on the planet, and research conducted by vpnMentor reveals how hackers managed to break into thousands of accounts using a rather simple technique.
This hacking approach allows them to use databases of exposed usernames and passwords, very often from other breaches, and try the credentials on a new target. The method works more often than you’d imagine, especially because a worrying number of users continue to stick with the same usernames and passwords for multiple online services.
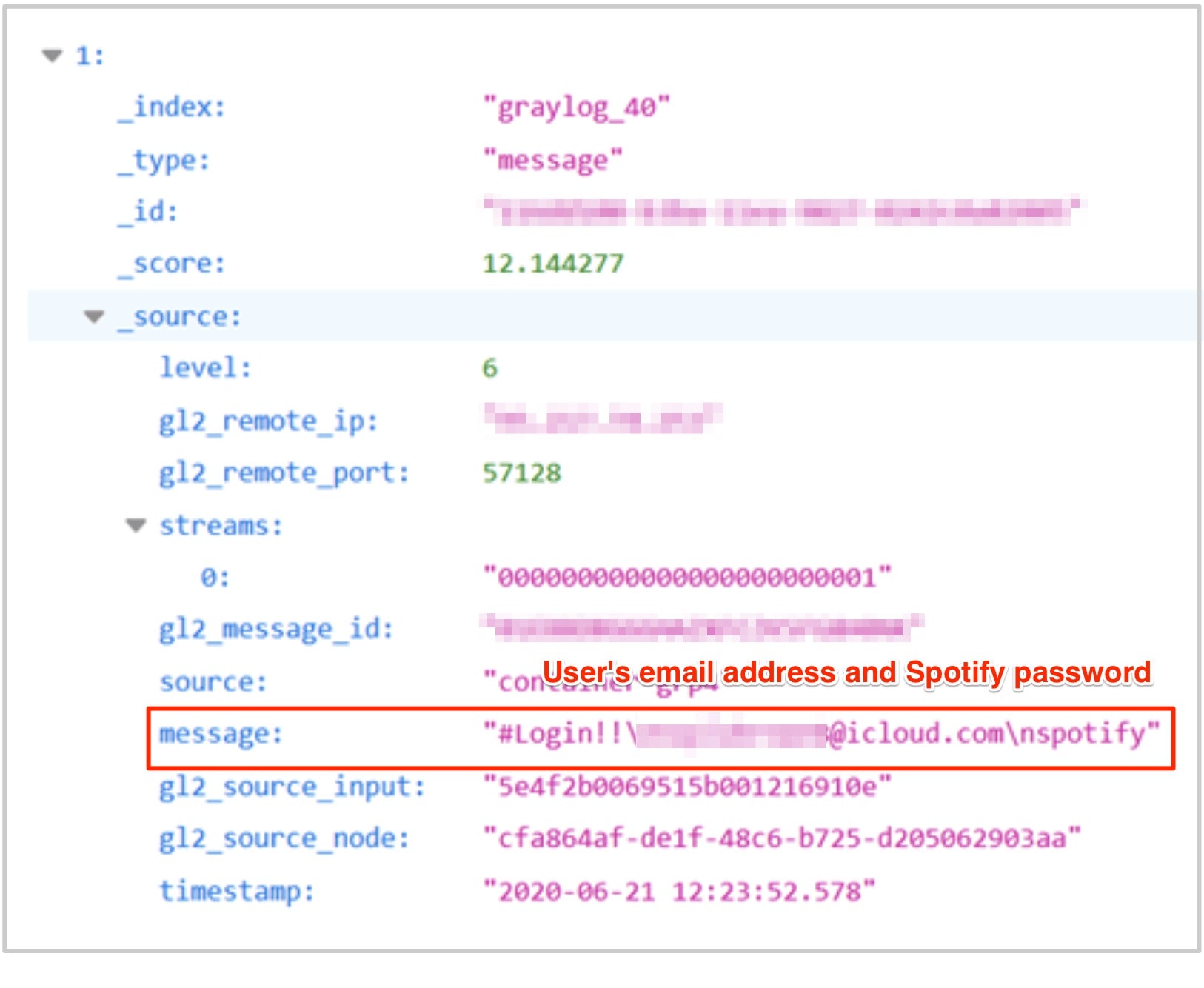
The research team came across an Elasticsearch database that included no less than 380 million records, and while its origins are unknown, it’s believed the credentials were obtained from other attacks.
The 72GB database was hosted on an unsecured server and included account usernames and passwords verified on Spotify, email addresses, and countries of residence. Personally Identifiable Information, or PII, has also been exposed, the analysis reveals, after the malicious actors likely obtained access to more than 300,000 accounts.
“The exposed database could be used in many criminal schemes, not just by the fraudsters who built it, but also by any malicious hackers who found the database, as we did. Any of these parties could use the PII data exposed to identify Spotify users through their social media accounts, and more. With this information, criminals could pursue several activities to defraud and hack Spotify users,” researchers warned.
There’s one big security concern though: Spotify does not support multi-factor authentication, a method allowing users to further increase the security of their accounts by adding a verification method based on text messages sent to their mobile devices or email. Spotify also hasn’t provided an ETA as to when such a security update could be rolled out for its service.
In the meantime, users themselves can protect their accounts, and the easiest way to do it is to use unique passwords for every online service. Even if one account is exposed following a breach, setting up a unique password means hackers wouldn’t be able to log in elsewhere with the same credentials, so overall, your other online accounts are fully protected.
And of course, complex passwords are always the right way to go, as they make it much harder for a long phrase including letters, numbers, and symbols to be hacked. Using a password manager makes the whole thing a lot more convenient, and there are tons of them out there, many with support for mobile devices, so you can have your credentials with you wherever you go.
Needless to say, if you used the Spotify login information to connect to other online accounts, you are strongly recommended to change it as soon as possible to prevent any other data breach that could occur and based on credential stuffing.
But this doesn’t necessarily mean Spotify is also the most secure service on the planet, and research conducted by vpnMentor reveals how hackers managed to break into thousands of accounts using a rather simple technique.
What is credential stuffing and how it was used against Spotify
First and foremost, security researchers explained that malicious actors didn’t launch a complex operation against Spotify users but actually relied on a method called credential stuffing.This hacking approach allows them to use databases of exposed usernames and passwords, very often from other breaches, and try the credentials on a new target. The method works more often than you’d imagine, especially because a worrying number of users continue to stick with the same usernames and passwords for multiple online services.
The research team came across an Elasticsearch database that included no less than 380 million records, and while its origins are unknown, it’s believed the credentials were obtained from other attacks.
The 72GB database was hosted on an unsecured server and included account usernames and passwords verified on Spotify, email addresses, and countries of residence. Personally Identifiable Information, or PII, has also been exposed, the analysis reveals, after the malicious actors likely obtained access to more than 300,000 accounts.
“The exposed database could be used in many criminal schemes, not just by the fraudsters who built it, but also by any malicious hackers who found the database, as we did. Any of these parties could use the PII data exposed to identify Spotify users through their social media accounts, and more. With this information, criminals could pursue several activities to defraud and hack Spotify users,” researchers warned.
Spotify’s response and how to protect your account
The Spotify security team was alerted of the issue in July and the company responded rather fast, eventually initiating a rolling reset of passwords for the affected users. In other words, users whose data was potentially exposed were forced to reset their passwords and thus protect their accounts.There’s one big security concern though: Spotify does not support multi-factor authentication, a method allowing users to further increase the security of their accounts by adding a verification method based on text messages sent to their mobile devices or email. Spotify also hasn’t provided an ETA as to when such a security update could be rolled out for its service.
In the meantime, users themselves can protect their accounts, and the easiest way to do it is to use unique passwords for every online service. Even if one account is exposed following a breach, setting up a unique password means hackers wouldn’t be able to log in elsewhere with the same credentials, so overall, your other online accounts are fully protected.
And of course, complex passwords are always the right way to go, as they make it much harder for a long phrase including letters, numbers, and symbols to be hacked. Using a password manager makes the whole thing a lot more convenient, and there are tons of them out there, many with support for mobile devices, so you can have your credentials with you wherever you go.
Needless to say, if you used the Spotify login information to connect to other online accounts, you are strongly recommended to change it as soon as possible to prevent any other data breach that could occur and based on credential stuffing.