SpaceX made a name for itself not only by offering internet access in places that lack basic utilities but also for its bulletproof security. During the Black Hat USA 2022, the latter shattered to pieces after a security researcher demonstrated how easy it was to break the Starlink terminals’ security.
Starlink’s internet service has proven invaluable for an internet connection during the Ukrainian war. The SpaceX service has also proved very reliable and successfully resisted several break-in attempts by Russian intelligence. This earned it the fame of being almost impenetrable until a security researcher demonstrated the opposite during the Black Hat USA 2022 security event.
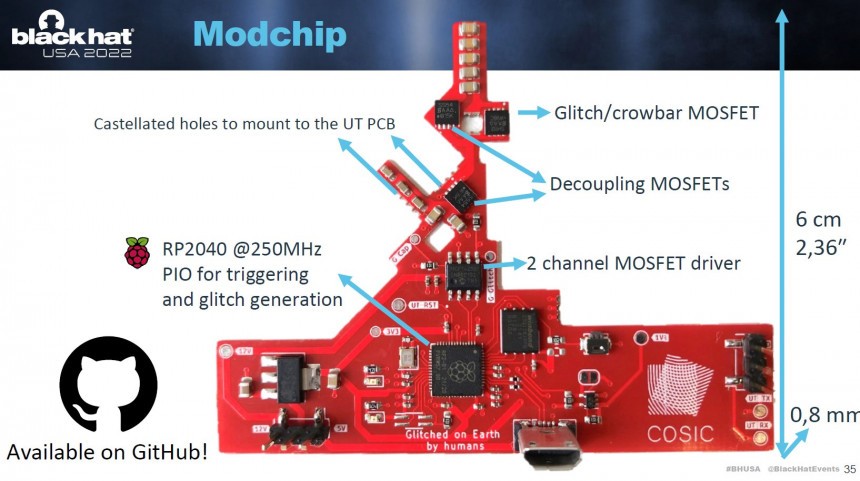
Lennert Wouters, a security researcher at the Belgian university KU Leuven, has demonstrated a successful method to access the Starlink system and run custom code on the devices. Wouters built a custom hacking tool that can be attached to any Starlink dish antenna. Interestingly, the black-box device was built using off-the-shelf components with a total bill of materials of less than $25. Once attached to the antenna, the device allows injecting the custom code and bypassing Starlink’s security protections.
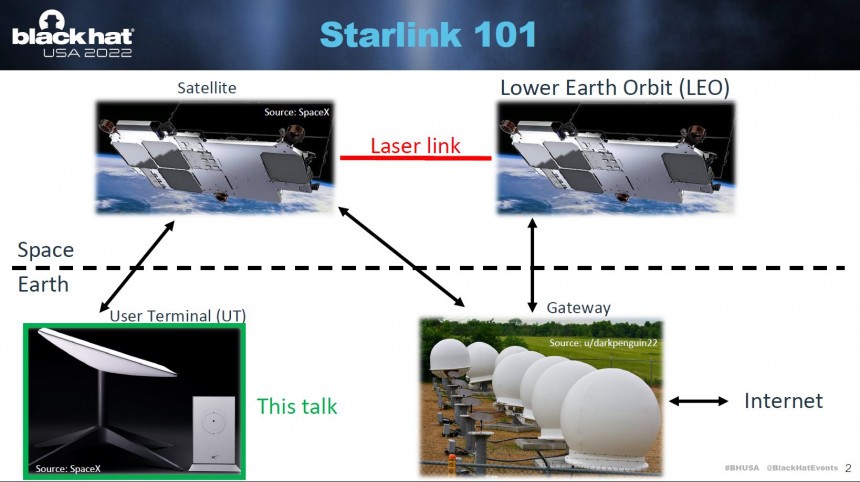
The hack is limited to the user terminals and requires physical access to succeed, but Wouters thinks it can be used to access a deeper section of the system. It could be used to get to the satellites themselves. That’s why he notified Starlink of the flaws last year, and SpaceX reportedly issued a software update to make the attack more difficult.
“As an attacker, let’s say you wanted to attack the satellite itself,” Wouters explained, “You could try to build your own system that allows you to talk to the satellite, but that’s quite difficult. So if you want to attack the satellites, you would like to go through the user terminal as that likely makes your life easier.”
Although Starlink has modified the terminal software, an attack can still be successful with a modified modchip. Unfortunately, the underlying issue cannot be fixed in software and requires SpaceX to replace the main chip. Until then, all user terminals are vulnerable, according to Wouters. But to be successful, the attack needs physical access, so Starlink customers are not in danger. On the other hand, the network might be because a hacked user terminal can be used as a gateway into the system.
Wouters explained that he is working now on accessing the backend servers. Following his demonstration at Black Hat USA 2022, SpaceX has issued a document describing how it secures the system. The company acknowledges the attack but thinks it cannot go further inside the broader system.
“We find the attack to be technically impressive, and is the first attack of its kind that we are aware of in our system,” the paper says, according to Wired. “We expect attackers with invasive physical access to be able to take malicious actions on behalf of a single Starlink kit using its identity, so we rely on the design principle of ‘least privilege’ to constrain the effects in the broader system. Normal Starlink users do not need to be worried about this attack affecting them, or take any action in response.”
Following his discovery, Wouters was hired by SpaceX to assist in enhancing cybersecurity. As more companies aim to create their own satellite constellations, satellite security will become increasingly important. SpaceX and Starlink don’t just provide home users with internet connectivity but also provide connectivity for the military and commercial sectors and play a role in critical infrastructure.
As Russian troops invaded Ukraine in February, alleged Russian military hackers targeted the Via-Sat satellite system on which the Ukrainian military relied. The system crashed, and around 30,000 internet connections in Europe were disrupted, including more than 5,000 wind turbines.
Lennert Wouters, a security researcher at the Belgian university KU Leuven, has demonstrated a successful method to access the Starlink system and run custom code on the devices. Wouters built a custom hacking tool that can be attached to any Starlink dish antenna. Interestingly, the black-box device was built using off-the-shelf components with a total bill of materials of less than $25. Once attached to the antenna, the device allows injecting the custom code and bypassing Starlink’s security protections.
The hack is limited to the user terminals and requires physical access to succeed, but Wouters thinks it can be used to access a deeper section of the system. It could be used to get to the satellites themselves. That’s why he notified Starlink of the flaws last year, and SpaceX reportedly issued a software update to make the attack more difficult.
Although Starlink has modified the terminal software, an attack can still be successful with a modified modchip. Unfortunately, the underlying issue cannot be fixed in software and requires SpaceX to replace the main chip. Until then, all user terminals are vulnerable, according to Wouters. But to be successful, the attack needs physical access, so Starlink customers are not in danger. On the other hand, the network might be because a hacked user terminal can be used as a gateway into the system.
Wouters explained that he is working now on accessing the backend servers. Following his demonstration at Black Hat USA 2022, SpaceX has issued a document describing how it secures the system. The company acknowledges the attack but thinks it cannot go further inside the broader system.
Following his discovery, Wouters was hired by SpaceX to assist in enhancing cybersecurity. As more companies aim to create their own satellite constellations, satellite security will become increasingly important. SpaceX and Starlink don’t just provide home users with internet connectivity but also provide connectivity for the military and commercial sectors and play a role in critical infrastructure.
As Russian troops invaded Ukraine in February, alleged Russian military hackers targeted the Via-Sat satellite system on which the Ukrainian military relied. The system crashed, and around 30,000 internet connections in Europe were disrupted, including more than 5,000 wind turbines.
#BringOnTheBugs - We love working closely with security researchers! Special shout-out to @LennertWo for an amazing presentation!https://t.co/jdhYaherNX
— Christopher Stanley ? (@cstanley) August 11, 2022
We are hiring! If you are a badass engineer and love space, please checkouthttps://t.co/Z6ha1EtgYE