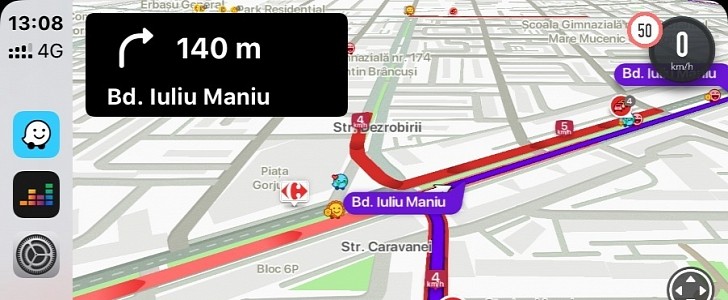
Waze is a fantastic app, there’s no doubt about it, and the millions of users who launch it every day to get around the nightmare traffic in their cities certainly agree.
But at the same time, it’s also not a secret that Waze needs additional improvements in some key areas, and it looks like the security offered to users is one of them.
More specifically, security engineer Peter Gasper discovered a vulnerability in Waze that allowed him to track a random driver on the map and see where they are going. It was all because of the way Waze is built in the first place.
When you use Waze, the app also shows the icons of other drivers that are around you. The researcher found out that when using the web interface of the app, he can request the Waze API to display the coordinates for both his location and for other nearby drivers. When inspecting the data returned by the API, the identification numbers (ID) associated with the icons were not only also included, but they didn’t change over time.
So the ID is unique to every user, which means you can track it to follow them on the map.
“I decided to track one driver and after some time she really appeared in a different place on the same road. I have spawned code editor and built Chromium extension leveraging chrome.devtools component to capture JSON responses from the API. I was able to visualize how users broadly traveled between the city districts or even cities themselves,” the researcher explains.
What’s worse than tracking one user on the map? Finding them who they really are. The researcher started looking for ways that would convert the username to an ID and eventually discovered another problem with the event reporting system in Waze.
“I found out that if user acknowledge any road obstacle or reported police patrol, user ID together with the username is returned by the Waze API to any Wazer driving through the place. The application usually don’t show this data unless there is an explicit comment created by the user, but the API response contains the username, ID, location of an event and even a time when it was acknowledged,” the security experts details in an August analysis of the vulnerability.
So theoretically, a hacker could have done the same thing, keeping an eye on users who confirm a specific report sent on Waze, only to discover their usernames. Once the username of a Wazer is determined, a malicious actor can scan public profiles and social media to determine the identity of a user.
The vulnerability was reported to the Google-owned company in December, and it was already patched. The security researcher received a $1,337 bounty for this report.
More specifically, security engineer Peter Gasper discovered a vulnerability in Waze that allowed him to track a random driver on the map and see where they are going. It was all because of the way Waze is built in the first place.
When you use Waze, the app also shows the icons of other drivers that are around you. The researcher found out that when using the web interface of the app, he can request the Waze API to display the coordinates for both his location and for other nearby drivers. When inspecting the data returned by the API, the identification numbers (ID) associated with the icons were not only also included, but they didn’t change over time.
So the ID is unique to every user, which means you can track it to follow them on the map.
“I decided to track one driver and after some time she really appeared in a different place on the same road. I have spawned code editor and built Chromium extension leveraging chrome.devtools component to capture JSON responses from the API. I was able to visualize how users broadly traveled between the city districts or even cities themselves,” the researcher explains.
What’s worse than tracking one user on the map? Finding them who they really are. The researcher started looking for ways that would convert the username to an ID and eventually discovered another problem with the event reporting system in Waze.
“I found out that if user acknowledge any road obstacle or reported police patrol, user ID together with the username is returned by the Waze API to any Wazer driving through the place. The application usually don’t show this data unless there is an explicit comment created by the user, but the API response contains the username, ID, location of an event and even a time when it was acknowledged,” the security experts details in an August analysis of the vulnerability.
So theoretically, a hacker could have done the same thing, keeping an eye on users who confirm a specific report sent on Waze, only to discover their usernames. Once the username of a Wazer is determined, a malicious actor can scan public profiles and social media to determine the identity of a user.
The vulnerability was reported to the Google-owned company in December, and it was already patched. The security researcher received a $1,337 bounty for this report.